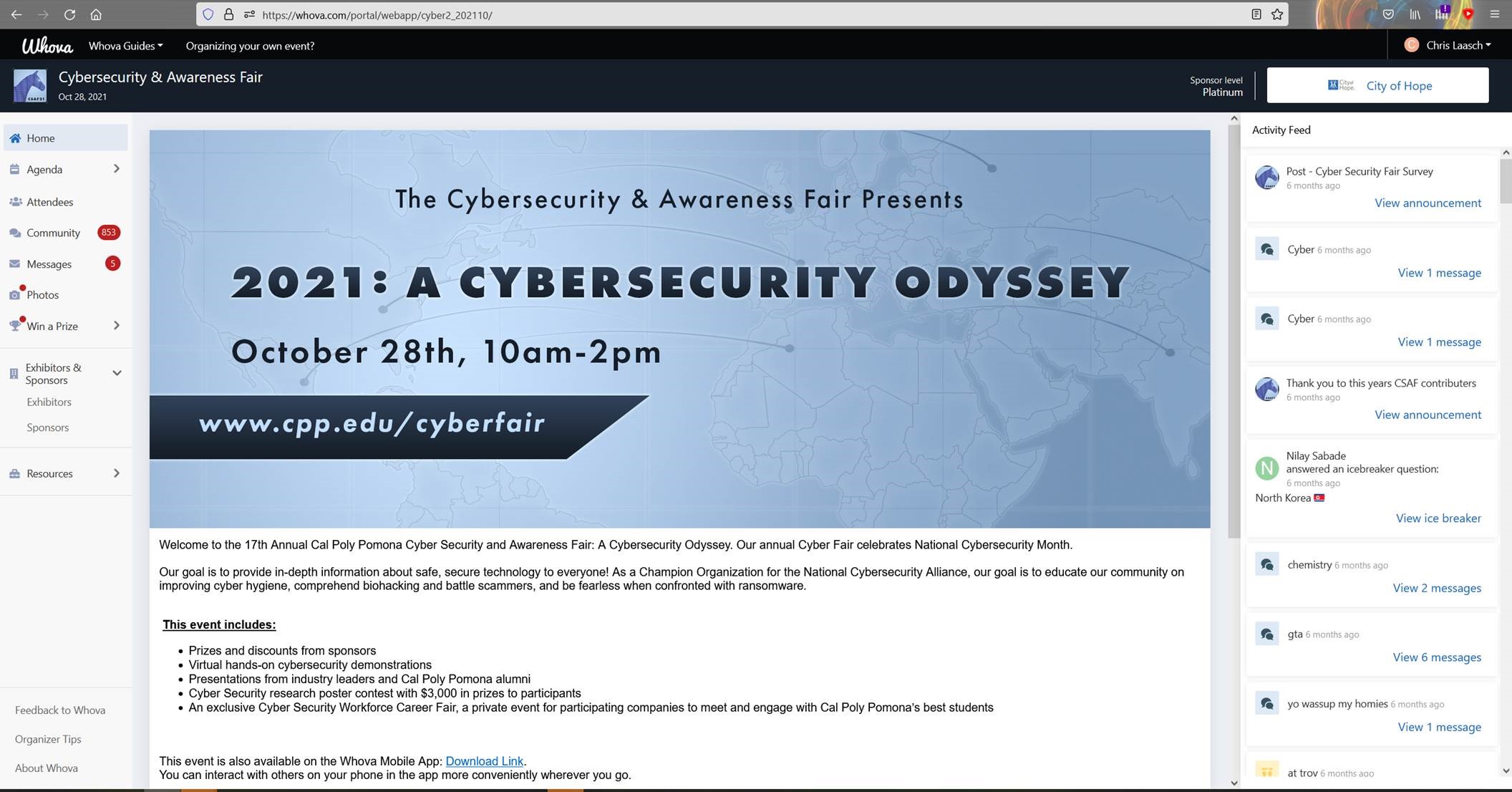
2021 Cyberfair
Theme: 2021: A Cybersecurity Odyssey

Tuesday, October 28th 2021

Event Summary
2021: A Cybersecurity Odyssey was the 17th year of CPP’s Cybersecurity and Awareness Fair, successfully presented virtually and hosted by Whova. Fair goers were able to use their mobile apps or browsers to access the online platform and view the different speaker sessions and presentations. Attendees from all over were also encouraged to network with each other, participate in various events and contests for a chance to win gift cards and vouchers. The fair’s presentations by students and industry professionals ranged from personal cyber safety, technical demonstrations, and career opportunities and growth such as “Phishing, A Deep Dive Into the Operation” by CPP’s SWIFT, “Microsoft 365 Defender” by Ash Sumer from Microsoft, and “Becoming a Cybersecurity Professional” by StoneTurn. This year also marked the launching of the Cyber Problem-Solving category, joining the Cybersecurity Awareness category in the poster contest. This year’s poster winners came from CPP and Fullerton College. In addition to the fair, the fourth annual Cybersecurity Workforce Job Fair hosted by Brazen allowed students to network with employers such as City of Hope, CrowdStrike, and StoneTurn. All presentations, demonstrations, and poster sessions were recorded on the day of the fair and were made available for viewing after the event.
Presentations
Presented by FAST
Biohacking has been a topic explored in science fiction and other stories for many decades. But due to recent breakthroughs in technology, these concepts are becoming more and more feasible for many of us. Cal Poly FAST (Forensics and Security Technology) plans to explore how personal medical devices are making their way into many people's everyday lives and how cyberattacks on these devices are an emerging threat. These attacks could target personal health information or even a person's current location. Our presentation will highlight vulnerabilities in continuous glucose monitoring devices, physical location tracked through Bluetooth, sensitive information exposed to anyone within the broadcast range, and educate everyone on what they can do to keep their data safe.
Presented by MISSA
Cyber hygiene is making intelligent decisions about your smart devices. Tools such as antivirus software, network firewall, and password protection are components that can reduce your risk and strengthen the security of your personal data and information. Cal Poly Pomona’s MISSA (Management Information Systems Student Association) will guide you through the best practices and benefits of keeping yourself cyber safe.
Presented by ./Script
Online privacy concerns have increased year after year, but many people ignore the consequences of not actively protecting their information. So much information about our lives is harvested, yet we have become accustomed to this invasion of privacy. Cal Poly’s ./script (Security, Cryptography, Reverse Engineering, Incident Response, and Penetration Testing) investigates how our online actions are being tracked, how our information is used against us, and how we can protect ourselves.
Presented by SWIFT
Approximately 75% of Global Organizations reported experiencing some form of phishing in 2020 alone. As cyber threats continue to grow, it is critical for the next generation of cybersecurity specialists to understand the anatomy of a phishing attack. Join us as Cal Poly Pomona’s very own SWIFT (Students With an Interest in the Future of Technology) demonstrates the development and tactics behind successful phishing attacks as well as defensive strategies to prevent them.
Presented by Chaffey College
Ransomware is an ever-evolving form of malware designed to encrypt files on your devices, turning them into hostages while making your devices unusable. Malicious actors then demand a ransom. The worst ransomware actors often target and threaten to sell or leak exfiltrated data or authentication information if the ransom is not paid. So, what does that mean for you? Hackers use weak security spots like the recent PrintNightmare vulnerability to steal sensitive data and/or lock files. These criminals will only give you the key to access your system, or return the files, once you’ve paid their ransom. Chaffey College will teach you the fundamentals to protect your data and help mitigate the risks associated with ransomware.
Speaker Sessions
Presented by William Perry, City of Hope
This presentation discusses his journey on becoming a Chief Information Security Officer at City of Hope.
Presented by Jeffrey Buccola, Deloitte
Your online identity is a valuable asset that is sought for marketing and for malicious purposes. Learn why it really does matter to protect your identity and what steps you can do to protect it from being compromised.
Presented by Cliff Maraschino, Protiviti
This presentation includes an overview of Protiviti and an overview of SIEM/SOAR and Quantum Cryptography.
Presented by Joe Lam, Irvine Ranch Water District
The presentation takes the audience into the Water Sector where it is transforming from traditional Operational Technology (OT) into the next generation. The presentation gives a short introduction into what is operational technology, SCADA (Supervisory Control and Data Acquisition) system, and PLC (Programmable Logic Controllers). The differences and similarities between IT & OT. The challenges and opportunities as IT & OT converge from a cybersecurity perspective and finally, how to make a hacker cry.
Presented by Dale Samsel, Assa Abloy
This session will focus on the lastest technologies, 802.3(PoE), 802.11(WiFi) & 802.15.4(Zigbee) that leading lock manfacture ASSA ABLOY is utilizing for access control.
Presented by Dr. Mary Dziorny, Accenture
Cybersecurity is a tech problem, right? Not exactly. The current threat landscape puts human targets in the forefront, meaning you are the first and last line of defense against the threat actors. In this session, we’ll talk about the most common current human-targeted cyber threats and what you can do to defend yourself and your family against them. We’ll also include some tips for those who want to pursue careers in the human side of security. The session will conclude with time for questions and answers.
Presented by Ash Sumer, Microsoft
This presentation discusses Microsoft's achievements in Gartner Magic Quadrant reports and Forrester Wave reports, M365 Defender Suite XDR, and other security products such as Azure Defender and Sentinel. The presentation concludes with an M365 Demo.
Presented by Ross Rustici, Daron Hartvigsen, and Nick Giacopuzzi from StoneTurn
This session will dive into how professionals get started in the field. As hiring managers with experience in the government, technology vendors, and consultancies, we will discuss: the attributes that stick out to us on resumes; the skills and intangibles we look for in candidates; and some of the non linear career paths that have produced exceptional talent. We will also discuss some of the more successful tactics to unlocking opportunities at firms like StoneTurn
Presented by Paul Warrick, AICPA
The presentation covers the AICPA CITP credential and Univeristy Program in IT. CITP credential topics include the body of knowledge, requirements, holder benefits, and the alignment with the AICPA University Program in IT. Resources are provided for faculty and students, and requriements for participating schools is discussed.
Presented by Dr. Richard Hays, CISA
CISA CSA Services - Supporting Incident Detection. Cyber Resilience Review (CRR) External Dependencies Management (EDM) Cyber Infrastructure Survey/Review (CIS) Information and Data Sharing Incident Management & Response Intrusion Detection requires Continuous Monitoring Know the Environment that you are protecting Tunning IOC's Ransomware
Presented by Tina Thorstenson, CrowdStrike
We’ll discuss Tina's journey to becoming a higher education technology leader, the current state of cyber security threats in higher education, things each of us can do to protect ourselves and our community, as well as share successful strategies for career advancement. With decades in industry and higher education, she’s passionate about protecting communities while leveraging innovative solutions, and has brought her combined expertise to CrowdStrike. Join the discussion as we forge the Power of We to stop the adversaries.
Presented by Warren Yu
Come learn about little-known federal internships, scholarships and jobs (many of them dealing directly with cyber security) that pay you during summers, for tuition, or to launch or redesign a career in a STEM-related field!
Poster Contest
Presented by Trong Nguyen, First Place in Cyber Problem-Solving Category
IoT has become one of the fastest-growing industries along with Artificial Intelligence and Machine Learning. Many people have at least one smart device in their house. Intelligent vacuum robot is one of the IoT devices that recently have gained public interest. Vacuum robot has been widely adopted, but its security has not been thoroughly evaluated. Researchers worldwide have been especially interested in exploiting vacuum robot's vulnerabilities, and it looks like they keep finding new flaws. In this paper, I would like to analyze the vacuum robot ecosystem to exploit vulnerabilities in a popular vacuum robot model that I found on Amazon. First, the vulnerabilities I found would be categorized under CIA triads and described under STRIDE threat modeling. After that, I suggested the manufacturers' mitigations to secure their devices to protect users' data.
Presented by Danica Cariaga and Amber Thomas, Second Place in Cyber Problem-Solving Category
Quantum computers are on track to break our current encryption algorithms. Having strong encryption standards is necessary to protect data for private communications, company data, military secrets, and other sensitive data. With quantum computers cracking algorithms, private data will be exposed, and can be used against victims in cyber and physical attacks. By finding quantum-resistant cryptographic algorithms, it will make it difficult for quantum computers to disrupt future encryption methods. Post-quantum cryptography aims to be compatible with classical and quantum computers. An important contribution to post-quantum cryptography is lattice-based cryptography. In this emerging field, post-quantum protocols must be developed with consideration for quantum key distributions and facilitating new research that collaborates with existing infrastructure and researchers.
Presented by Mario A. Peraza, First Place in Cybersecurity Awareness
The fifth generation mobile network (5G) has the capability to be one hundred times faster than that of its 4G predecessor, has a stronger connection and a lower rate in the time it takes to capture, transmit and process data (latency). 5G networks allow the use of new mobile applications like those installed in your vehicle or those installed on your mobile phone to monitor your health. But, one must consider how all of these improvements affect the vulnerability of mobile device users. Faster speeds over 5G also mean that malicious attackers can deploy more attacks against our devices. Increased compatibility with applications also means that attackers have access to more data and sensitive information than ever before. As with all aspects of mobile security the human factor plays a huge role. People inadvertently aid attackers in obtaining access to information. 5G in itself offers additional protections in the form of encryption. Human behavior also has to be changed in order to keep attackers away from personal and sensitive data.
Presented by Edwin Ly and UyenNghi Nguyen, Second Place in Cybersecurity Awareness
Why is the cybersecurity industry failing? We’re failing the name of cybersecurity. Companies expect their information to be secure. But what happens? Their data is stolen. Their information isn't secure. Cybersecurity companies profit off of data not being secure. What’s the point of the industry if it doesn’t do anything to stop attacks from happening? What can we do in order to change this?
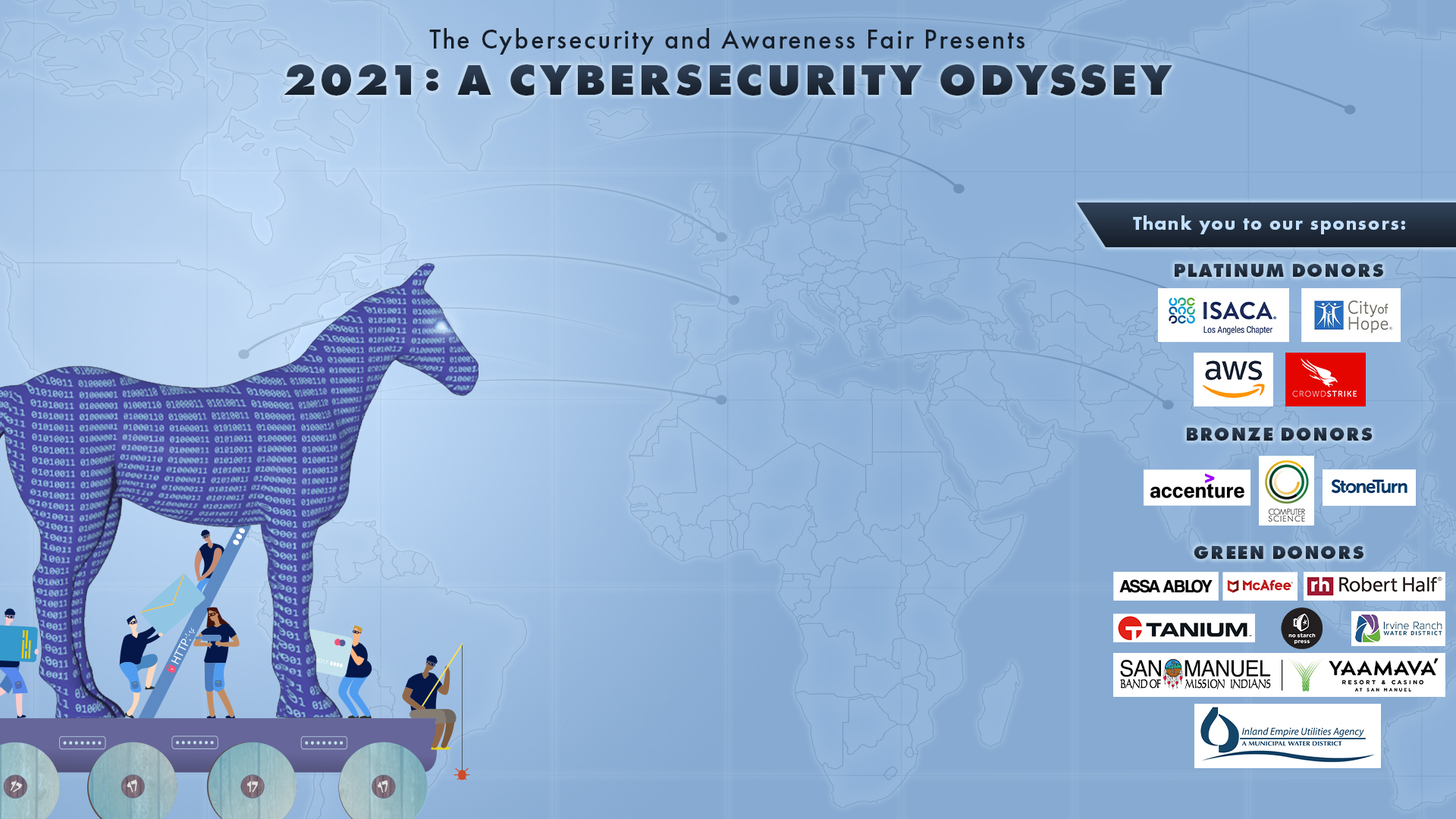
Sponsors
We would like to thank our wonderful sponsors for donating to help bring awareness to Cyber Security and the Information Technology Field.
Platinum Donors
Bronze Donors
Green Donors
Virtual Format
This years event was hosted on Whova, and had attendees log on to the moble app or on the desktop site shown below.