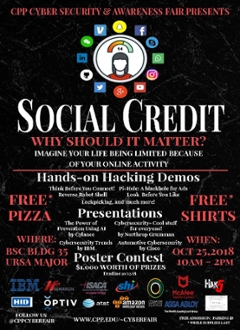
2018 Cyberfair
Theme: Social Credit- Why should it matter?
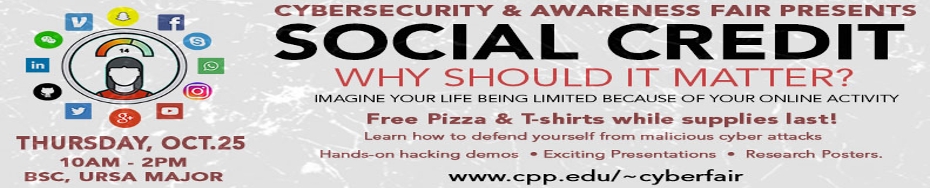
Thursday, October 25th 2018
Event Summary
The 14th edition of the Cyber Security and Awareness Fair was a successful journey with Social Credit. Over 500 participants ventured in from Fullerton College, Coastline, Chaffey, and Charter Oak High School along with Cal Poly Pomona faculty, staff, and students. This year’s fair is focused on Social Credit, inspired by China’s ‘Once Untrustworthy, Always Restricted’ Social Credit System. According to the Supreme People’s Court of China, 6 million Chinese citizens had already been banned from airplane flights for social misdeeds in early 2017; this number will only grow. How does this apply to cybersecurity? We have Internet-connected devices in our homes, cars, pockets, and even on our wrists – the data gathered by these devices is used to build a profile of the user that can be abused – not only by
Presentations
Live Demonstrations
| Presentor | Topic | Description |
|---|---|---|
|
MISSA
|
Look Before You Like
|
In this experiment, MISSA ran an analysis on comments from Facebook that include keywords, such as “Trump” or “immigration”, and the program sorts through a dictionary that categorizes the surrounding words as positive or negative. Participants were informed of how much information a third party could grab off you through an API on Facebook
|
| SWIFT | Think Before You Connect | SWIFT explored the uses of Hak5’s WiFi Pineapple and Packet Squirrel demonstrating how vulnerable your data can be to our attendees. |
| FAST |
Your Smart TV, Smart Toys, & IoT Devices are Spying on You. |
Attendes learned how to block advertisements, spying "analytics" companies, stop your SmartTV from spying on you, and got insight into the mysterious activity of IoT devices on your network, using a <$100 mini computer with free and open-source software! |
| Chaffey | Remote Robot Shell | Chaffey demonstrated how malicious hackers can run scripts on your computer using an innocent looking USB Rubber Ducky. They simply load the script onto the device and plug it into your computer; the scripts are run automatically by your computer. This functionality can be leveraged to create a reverse command shell that allows hackers to run programs on your computer, in addition to many other attacks. |
|
Fullerton College |
Haven Security Application |
Attendes were introduced to the Haven Security Application. Haven allows you to see who and when someone has touched your personal belongings . |
|
Charter Oak High School |
Bypassing Windows 10 Logon |
In this demo, Charter Oak showed how the Windows 10 login screen can be bypassed by a malicious hacker in order to access your personal data—and just how easy it is to do so, with tools like konboot and ophcrack. |
| Datagram | Lockpicking |
Atendees learned how to lock pick common household and TSA approved locks making them think twice before deciding what locks to use to secure their items. |
Sponsors
We would like to thank our wonderful sponsors for donating to help bring awareness to Cyber Security and the Information Technology Field.
Platinum Donors
Gold Donors
Bronze Donors